Security Salt and Hash
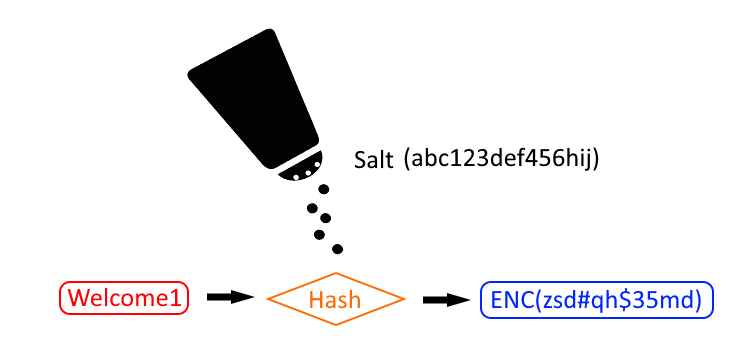
In Myst Studio 6.6.0 (introduced in rc2) there were password security enhancements to how Myst encrypts passwords. This article explains the changes to the enhanced password encryption.
Before and After Password Security Enhancement
Before 6.6.0 (rc2)
In previous versions passwords were encrypted in AES format seen as:
my.custom.password={AES}AZ12azasfdASDF9876asdf\=\=
After 6.6.0 (rc2)
Passwords are now hashed with a salt and seen as:
my.custom.password=ENC(abcZYX123!@#abcABC123)
Some additional points to be aware of:
- A salt (file) is generated on initial startup and used to hash Myst password properties.
/opt/Myst/data/key - On initial startup the Myst studio database populates an entry to flag that a salt has been generated. This prevents a new salt file being generated and overwriting the previous.
What does this mean for existing users?
Users upgrading to the new password security enhancement will find their existing passwords remain {AES} encrypted. To use the new salt, simply update existing password properties and Myst will use the salt and hash the password as ENC().
Importance of Backing up the key
It is important backup the key as it is uniquely generated on initial startup.
Every password which is encrypted using the key can only be decrypted correctly using the same key.
Extracting the key for backup purposes
Use below commands to view the key contents.
Note: The key file supports 15 characters with no new line character.
# Print the key contents to standard out
docker exec -ti Myststudio_web /bin/bash -c 'cat /opt/Myst/data/key'
# Copy the key file
docker cp Myststudio_web:/opt/Myst/data/key /tmp/key'
Creating the key for backup purposes
Alternatively you can create the key. Remember, no new line character.
# The -n prevents a new line
echo -n abc123def456hij > key
# Validate the key has 15 characters (and no new line character)
wc -c key
# The result should be:
15 key
The Master key
A salt (also referred to as the key) is used to encrypt and decrypt passwords.
Where is the key?
The salt is placed in a file named "key" located inside the Myststudio_web docker container.
Myststudio_web:/opt/Myst/data/key
When performing actions, Myst will copy the key onto the filesystem $Myst_HOME/key in order for Myst CLI to access.
How is the key file mounted?
The key file location is mounted using docker volumes part of the docker image. You do not need to do anything. Upgrading or recreating the container does not affect the key file as it is persisted. If you delete the docker volume then the key will be deleted.
Execute the command docker inspect Myststudio_web, to see the volume location.
"Image": "Myst-studio",
"Volumes": {
"/opt/Myst/data": {},
"/usr/local/tomcat/conf/fusioncloud/ext": {},
"/usr/local/tomcat/conf/fusioncloud/license": {}
},
What does this mean for new users?
After installing Myst studio and starting for the first time a salt will be generated and all passwords are encrypted using the salt. It would simple be a matter of ensuring the /opt/Myst/data/key salt (file) is backed up in a secure repository.